Hello!
Today, we will create a small mobile application, which requires user authentication, using .NET MAUI.
I hope you already have a valid environment. Read this article on how to set up .NET MAUI.
If you don't have an Azure Active Directory, watch this video on how to set it up:
And Azure Active Directory (B2C):
So let's start!
Create a new .NET MAUI project.
Install
Microsoft.Identity.Clientpackage: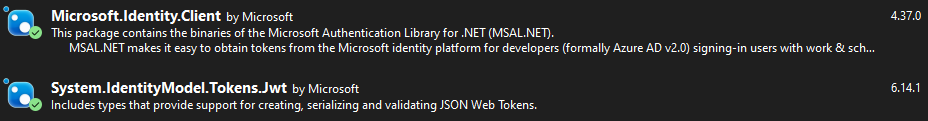
If the library doesn't work on iOS/MacCatalyst, you can still use .NET MAUI WebAuthenticator.
Create
Constantsclass:
Then modify manifest files.
For Android openAndroidManifest.xmland add the next activity to the application:
Pay attention that data android:scheme starts with msal.
For iOS add the following code to the Info.plist:
It allows the app to correctly work with Microsoft Authenticator if a user has MFA enabled.
We need to override some methods to receive a callback from the identity server.
For Android open Android/MainActivity.cs and override OnActivityResult method:
You also need to set the activity attribute Exported = true.
For iOS open iOS/AppDelegate.cs and override OpenUrl method:
It's time to create our
AuthService:
Now we can prepare the UI to use our AuthService.
Add login button to your XAML and add Clicked event handler:
We are done. Start the application and check the result.
The full code can be found on GitHub.
MauiAuth Blazor sample GitHub.




